
We believe in securely connecting everything by enabling users to build private networks within the internet that only they can see. We provide zero trust IT/OT networking as a service.
Language
English
日本
A recent security incident involving DJI robotic vacuums revealed how a single authentication weakness inside a centralized cloud control plane can expose thousands of devices globally. The problem was not just misconfigured credentials. It was architectural. When remote access depends on centralized brokers, publicly reachable APIs, and broadly scoped tokens, a small failure scales into systemic risk. A zero trust, service level connectivity model such as remote.it removes public exposure, binds identity directly to individual services, and eliminates lateral movement by design.
A security researcher recently uncovered a flaw in the remote access architecture of DJI robotic vacuums that allowed access to thousands of devices. As reported by The Verge, weak authentication controls within centralized cloud infrastructure enabled visibility into device telemetry and camera feeds at scale.
At first glance, the story reads like another consumer IoT security lapse. Connected home devices have long struggled with poor credential hygiene and inconsistent cloud security practices. However, this incident highlights a much deeper issue that extends well beyond consumer robotics. It exposes a structural weakness common across many IoT, industrial, and edge architectures: centralized trust.
The vacuums communicated through a cloud based control plane. Devices established outbound connections to a central service, which mediated commands, telemetry, and user authentication. This pattern is widely used because it simplifies deployment. Devices avoid inbound firewall rules. Operators gain centralized visibility. Users interact through a single interface.
The flaw emerged when authentication controls within that shared infrastructure proved insufficient. A single credential pathway opened access into the control layer. Once authenticated, the researcher could access data across a large fleet of devices. The issue was not limited to one endpoint. It scaled horizontally because the architecture itself was centralized.
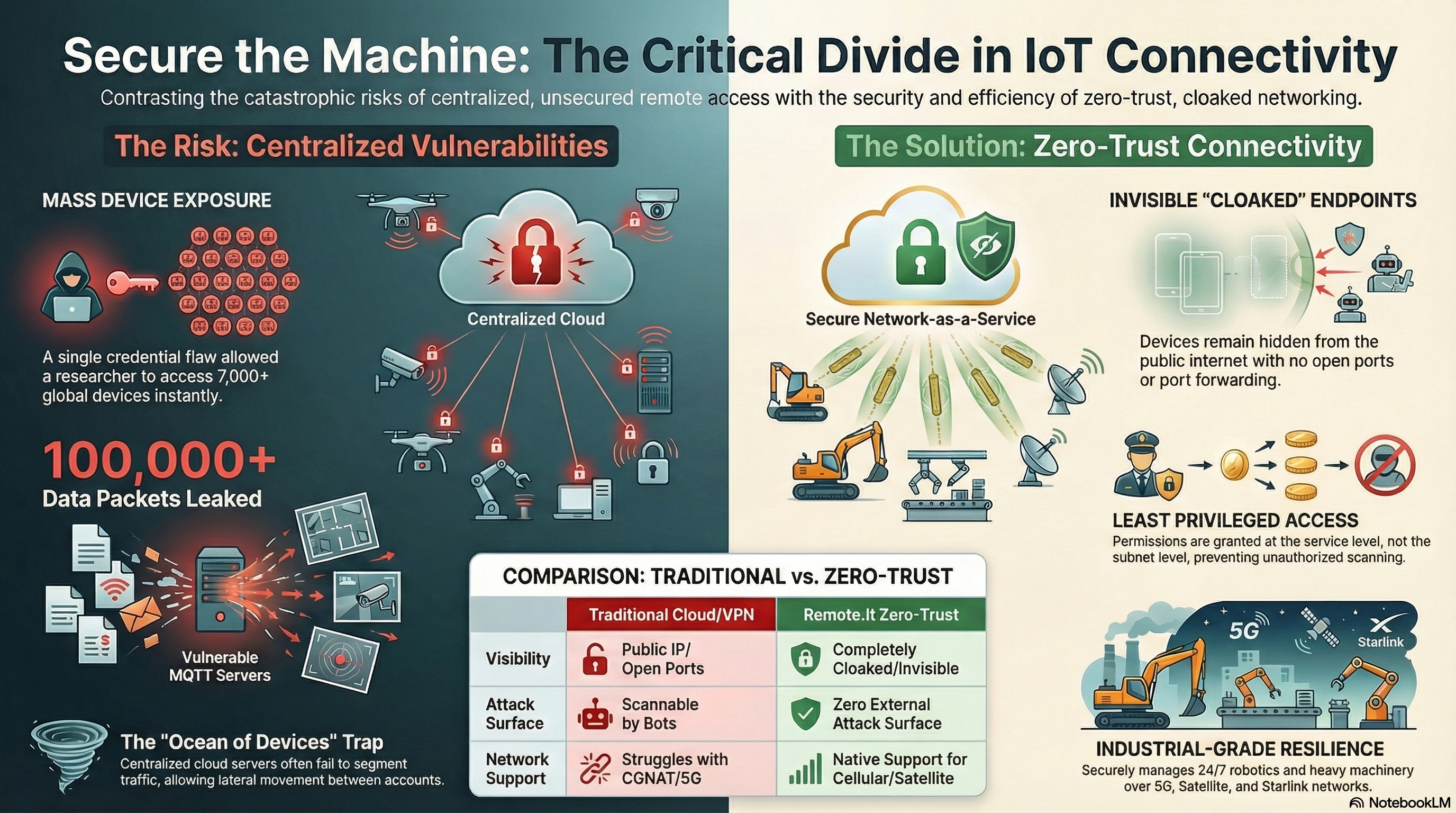
Centralized control planes introduce an inherent amplification effect. If identity and authorization are enforced at a shared cloud broker or API layer, then compromise at that layer affects every connected endpoint.
Many IoT systems rely on messaging brokers, often MQTT based, that aggregate device communication. These brokers route commands and telemetry between users and devices. If authentication tokens or account permissions are too broad, isolation between devices collapses.
In such environments, segmentation depends entirely on application logic. If that logic fails, the system behaves like a flat network behind a cloud façade. Attackers who gain entry into the broker layer can potentially enumerate devices, subscribe to telemetry streams, or issue commands across accounts.
The DJI incident illustrates this “ocean of devices” problem. Once inside the centralized system, device level isolation proved insufficient. The blast radius extended across thousands of units because the trust boundary existed at the wrong layer.
This pattern is not unique to consumer IoT. Enterprises deploy similar architectures for edge servers, industrial robotics, retail infrastructure, and remote branch systems. The control plane may differ in branding, but the architectural model remains the same: devices connect upstream to a shared service that mediates remote access.
If that service becomes vulnerable, the entire fleet inherits the vulnerability.
Even when devices initiate only outbound connections, centralized architectures frequently expose APIs, authentication endpoints, or broker interfaces to the public internet. These surfaces become targets for credential stuffing, enumeration, and token replay attacks.
The absence of inbound device ports does not eliminate exposure. It shifts exposure to the cloud tier.
In the DJI case, the vulnerability did not require physical proximity or firmware exploitation. It required interaction with centralized infrastructure that was reachable and improperly protected. The attack surface existed because the control plane existed as a shared, internet facing entity.
Note: You can segregate internal traffic in centralized cloud and data center environments using noBGP. noBGP creates secure virtual networks than can span physical and logical (not a VLAN) networks.
As fleets grow, that surface becomes increasingly attractive. An attacker who compromises one control layer gains leverage over thousands of endpoints.
Traditional remote access solutions often rely on network level trust. VPN gateways, port forwarding, and subnet based access control grant users adjacency to entire network segments once authenticated.
This model assumes that the perimeter is defensible and that authenticated users behave correctly. In practice, credentials leak, tokens expire incorrectly, and misconfigurations occur.
When network level trust underpins remote connectivity, compromise grants broad reachability first. Authorization checks happen after adjacency exists. Lateral movement becomes a real risk.
The DJI incident demonstrates a related failure mode. Instead of a VPN, the trust boundary existed at a centralized cloud service. Once authentication succeeded, isolation controls proved inadequate. The result mirrored a flat network with insufficient segmentation.
Modern distributed systems cannot afford flat trust models, whether on premises or in the cloud.
A zero trust architecture redefines the trust boundary. Instead of asking whether a user may access a network, it asks whether a specific identity may access a specific service. There is no implicit adjacency and no subnet level permission.
remote.it implements this service level approach. Devices establish outbound encrypted connections, but they do not expose public IP addresses or open ports. Services remain cloaked behind NAT, cellular networks, or private addressing schemes. There is no internet visible endpoint to scan.
Each service registers independently and binds to a unique identity. Access policies attach directly to that service. A credential grants access only to explicitly authorized endpoints, not to an entire fleet or subnet.
This architectural difference matters when something goes wrong. If a credential is misused, the blast radius remains constrained to the service it was authorized for. There is no shared broker namespace to enumerate and no centralized device pool to traverse.
In effect, the attack surface approaches zero because there is nothing externally reachable to attack.
The DJI vacuum story captured attention because it involved camera feeds in consumer homes. The same architectural weaknesses exist in industrial and enterprise environments where the consequences are far more severe.
Manufacturing facilities connect robotic systems over 5G and satellite links. Energy operators manage remote assets across wide geographic regions. Retail chains deploy edge compute nodes in every location. Many of these environments still depend on VPN concentrators, public cloud brokers, or port forwarded services.
If a centralized authentication layer fails in these contexts, the impact can extend beyond data exposure to operational disruption.
By removing public exposure and eliminating subnet level trust, a service level connectivity model prevents such systemic escalation. Devices remain invisible to the internet. Connections require explicit identity validation. There is no ambient network to explore.
This model aligns security with how modern systems actually operate. Workloads are distributed. Networks are unpredictable. Identity must become the primary enforcement mechanism.
Security improvements often introduce operational burden. Complex certificate management, firewall rules, and VPN configurations create friction for engineering teams.
A cloaked connectivity model simplifies these operational tasks. Devices initiate outbound connections. No inbound firewall rules are required. There are no public IP addresses to provision or manage. Service registration defines connectivity, and identity defines authorization.
By eliminating manual network configuration steps, organizations reduce misconfiguration risk. Fewer moving parts mean fewer opportunities for subtle exposure.
In contrast, centralized cloud architectures frequently demand careful coordination of broker permissions, API scopes, and network security groups. Each configuration surface becomes another potential weak link.
The most important takeaway from the DJI incident is architectural humility. Systems should assume that credentials will eventually leak and that software will eventually contain defects. The only reliable mitigation is to constrain blast radius through design.
Centralized cloud mediated remote access concentrates risk. A failure at the control plane scales globally. Service level zero trust connectivity distributes trust and limits exposure.
When remote access architecture eliminates public IP reachability, removes subnet level trust, and binds identity directly to individual services, small mistakes remain small.
The consumer IoT sector often learns these lessons after high profile disclosures. Enterprises and industrial operators have the opportunity to apply them proactively.
The next headline about exposed devices will not hinge on encryption strength. It will hinge on whether architecture amplified or constrained a failure. Designing systems where services are invisible, connections are explicit, and trust is granular ensures that a single credential can never expose the world.